The rally may have paused, but the bull market is far from over. With the stimulus of price fluctuations, so does the activity, and the likelihood of mistakes in all the madness increases considerably.
Don’t worry! Security tools have improved significantly since the last cycle, and the industry’s understanding of attack vectors and vulnerabilities has improved.
The following are some things to keep in mind to improve security.
Wallet hygiene
Wallet hygiene is essential to protect your on-chain assets…… But what is it?
In general, wallet hygiene refers to developing good habits of using different wallets for different purposes. Your high-value NFTs and large token holdings should be stored in a more secure wallet than the one you use for shitcoin trading.
However, in some cases, you’ll be tempted to put your high-value assets at risk, for example, when you need to verify ownership of an asset to join a community, or take advantage of the nature of large wallets to earn airdrop rewards.
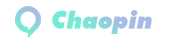
Delegate.cash (delegate.xyz) is a popular delegated option, which is the process of extending the permissions of one wallet to another, ultimately keeping your assets in a more secure state.
In addition to delegation, regularly cleaning and inspecting your cold wallets, hot wallets, browser wallets, and hardware wallets are all part of a robust crypto hygiene routine.monitorHow do you know what’s going on in your wallet?As users, we are aware of the changes that are happening in the wallet when we are actively transacting, exchanging, and sending, but you may be surprised to learn that a lot of things are happening on-chain that we didn’t know about.Some activity can be benign, like spam NFTs being sent to your address, but there are also occasional unknown activities that are worrying. Regularly monitoring the status of your wallet is an important part of keeping your assets safe in the long run. Companies like Webacy (Hi I’m the CEO!) can make monitoring easy by sending text messages or emails in real-time when activity is happening in and around your wallet.Pre-trade researchWe’ve all been there. You see everyone making money on tokens that skyrocket 1000% overnight, and you want to be a part of it too. You see a link and click on it. Your browser wallet pops up and prompts you to connect, then …… This is where many errors occur.In addition to the excitement, it can be difficult to pause to assess the security of the transaction you’re about to sign. Often, the transaction itself is difficult to interpret and may even be malicious.
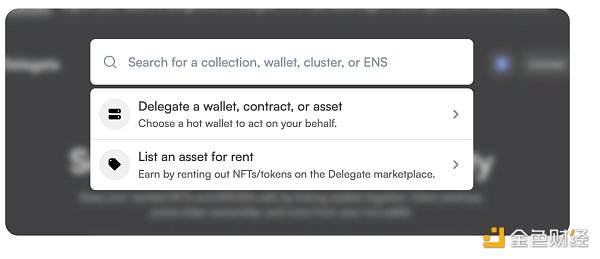
Browser extension tools can help users evaluate transactions before they happen, including Pocket Universe, Fire, and Wallet Guard, among others.
In recent years, the wallets themselves have also taken on more responsibility for user security by integrating additional security features. Phantom Wallet has a great user interface that shows changes in the state of the wallet after a transaction, making it easy for users to make informed decisions. Other wallets are also experimenting with their own security enhancements, but with mixed reviews.
If possible, you’ll need to evaluate the team behind the project, the contract itself, and the project’s historical success rate before jumping in blindly.
Approve and review
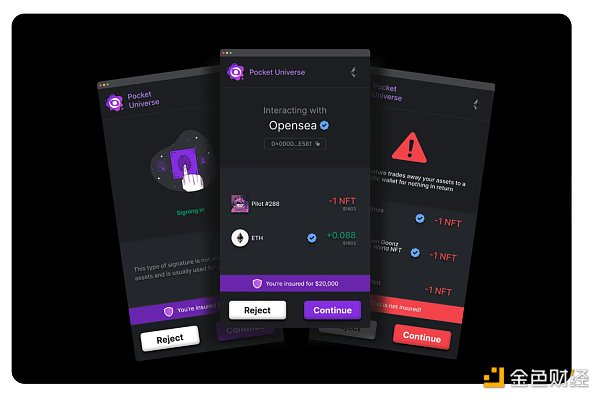
When you transact on-chain, you’ll usually need to grant permission to other addresses to spend your tokens and NFTs. These licenses are called “approvals”. These licenses are often necessary, but can sometimes be out of scope or even malicious.
If you’ve been using your wallet for a while, or are just very active, you should check your open permissions regularly. While tools like Revoke.cash or Etherscan’s token approval service are great, they don’t provide users with information on which approvals are good or bad. Our revocation feature provides both native revocation functionality and the ability to assess which open approvals are potentially dangerous to your wallet.
Traditional cybersecurity
We must not forget that traditional cybersecurity (OpSec) is critical to the overall security of crypto assets. After all, everything needs to be online.
The common culprits highlighted here are the reasons that cause many users to fall victim to hacks and scams. Take the time to check your system – don’t be the next person to hit the trending topic on Twitter.
- SMS verification codes (SMS 2FA) are no longer reliable. Sim swapping has become a major topic in crypto security and a playbook for hackers to follow. In all accounts that support other methods, remove your phone number from the two-factor authentication option.
- Password managers and cloud storage providers aren’t a safe haven for your logins or seed phrases. Through hacking or a data breach by the company itself, this information can be exposed, putting you at risk.
- Bookmark the most frequently visited encrypted websites to avoid phishing link scams.
- Turn off your Discord DMs.
There’s a lot more to be aware of, but just following these few steps will ensure that you’re not a good target.
Use items that care about the safety of your users
One last thing to note is to choose companies and projects that care about the safety of your users. Now that mature solutions are in place, such as embedded security APIs, there’s no reason why projects shouldn’t provide additional protections for their end users.
Self-hosting means that users need to take on more responsibility to protect themselves, but self-security is only part of the equation. It is also the responsibility of the project owner to utilize newly developed risk mitigation tools to protect the end user and, ultimately, the health of the company.
Companies like Mintify are actively taking steps to integrate security measures directly into their platform – a clear indication that they care about the safety of their end users.
Distributed security means a more secure Web3
Decentralization – a buzzword in the blockchain space and one of the cornerstones of such a great cryptocurrency. It must also be applied in terms of safety and security. If data and ownership are no longer controlled by a central entity within the walled garden, then the security and ownership of that data is also not controlled.
As control shifts to users and the companies that build networks for them, risk mitigation and security will become a category, improving together to address emerging challenges and use cases.